Blog Posts
View All Blogs →The Rise of Cybercrime: Cyber Attacks Reasons and Prevention Methods
Cybercrime is rapidly evolving, posing serious threats to individuals, businesses, and governments. That's why understanding the reasons behind cyber attacks and adopting effective prevention methods is crucial.
The Battle of Encryption: Symmetric vs. Asymmetric Cryptosystems Explained
Did you know that symmetric encryption is faster with a single shared key, while asymmetric encryption uses key pairs for enhanced security.
Types of Network Topologies with Examples
Discover how to safeguard your digital world—read on to learn the essential network security methods every user should know!
10 JavaScript Tricks Every Developer Should Know
Master these powerful JavaScript techniques to write cleaner, more efficient code and solve complex problems with elegance.
The AI Revolution: How AI Tools Are Enhancing Developer Productivity
Artificial Intelligence is no longer just a buzzword—it's becoming an essential part of the modern developer's toolkit.
With AI handling routine coding and debugging, developers can now focus more on creativity and solving complex problems. Many intelligent tools are not just speeding up development—they're redefining what's possible in software engineering.
Docker vs Kubernetes: What Developers Need to Know
Want to streamline your development workflow and master container orchestration?
Read the full article to understand how Docker and Kubernetes work together—and why they're essential tools for today's developers.
How to Use WebAssembly to Boost Your Web App Performance
You should learn how WebAssembly enables near-native performance in web apps by running code faster and more efficiently than traditional JavaScript.
Top 10 Ethical Hacking Tools For Every Security Enthusiast
Explore the top 10 ethical hacking tools that every security enthusiast should master to protect and test systems effectively.
Online Tools
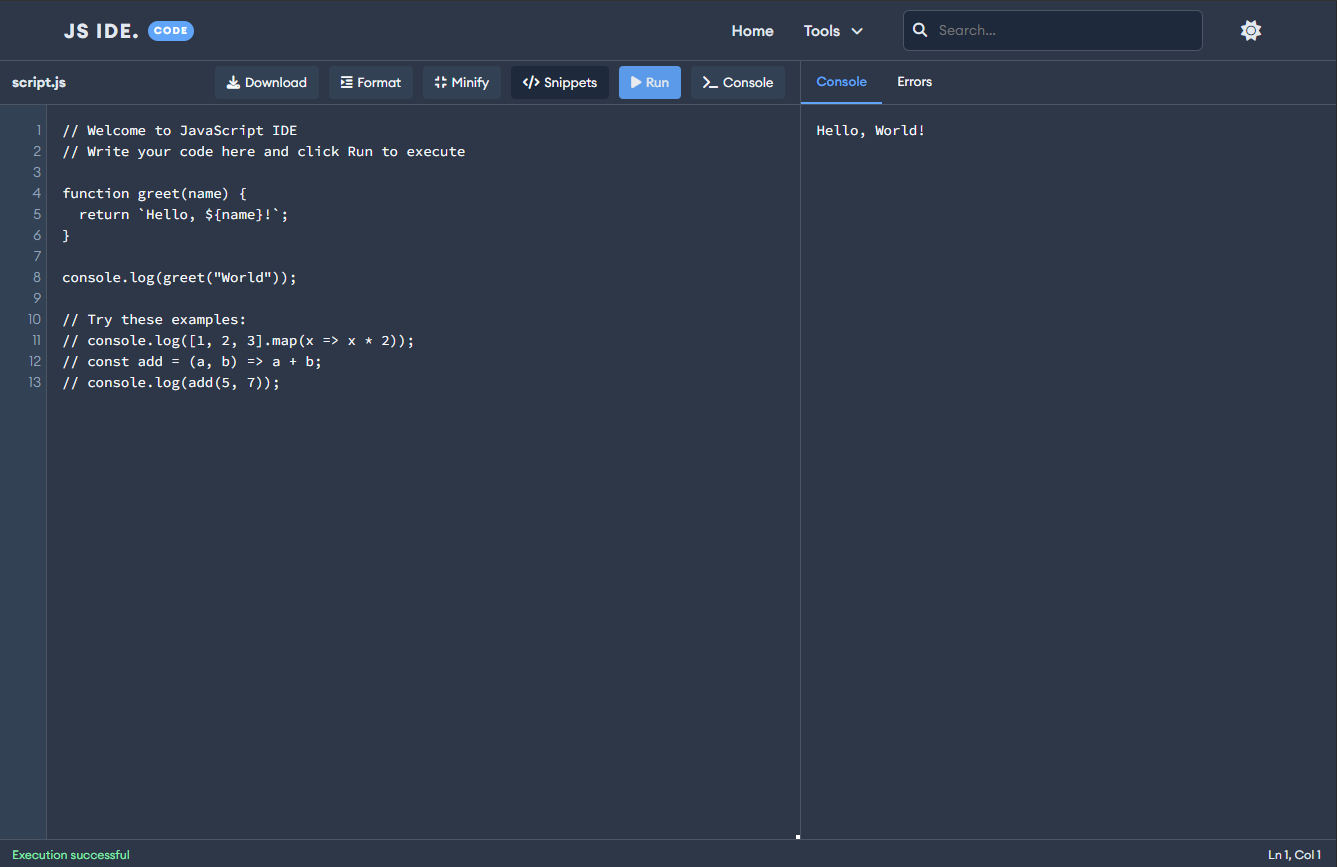
View All Tools →JavaScript IDE
Your powerful online JavaScript development environment with real-time execution and code formatting tools.
Features
This editor features a clean, minimalist interface designed to boost your coding productivity. It also includes built-in plugins that enhance and streamline your JavaScript development.
- User-friendly Layout
- Effortless Code Execution
- Code Prettify & Minify
- Code Snippets
- Quick Error Hunting