Cryptography
In networking and telecommunications, the data is transmitted over a network in such a way that if the data is captured, it cannot be read by unauthorized users. Cryptography comes from the Greek words "secret writing". It has a long and colorful history going back thousands of years, and its the science of information security. Cryptography also closely related to the disciplines of cryptology and crypto-analysis.
• Cryptology: It is the mathematics, such as a number theory and the application of formulas and algorithms.
• Crypto-analysis: It refers to the study of ciphers, ciphertext to find weaknesses in them that will permit retrieval of the plain text from the ciphertext, without necessarily knowing the key or the algorithms.
Cryptography includes techniques, such as micro-dots, merging words with images, and other ways to hide information in storage or transit. However, cryptography is most often associated with scrambling plain test (ordinary text) into ciphertext (a process called encryption), then back again (known as decryption). Cryptography is a tool that can be used to keep information confidential and to ensure its integrity and authenticity. Individuals who practice this field are known as Cryptographers.
Cryptographic techniques allow a sender to dis-guise the date so that an intruder can gain no information from the intercepted data. Cryptography involves two corresponding processes. These processes are described as under:
1. Encryption: Encryption is the process of converting plaintext into ciphertext (encoded, unreadable data) using an algorithm and a key.
2. Decryption: Decryption is the process of converting ciphertext back into plaintext, using the appropriate key and algorithm.
In both Encryption and Decryption are performed using algorithms and keys. An algorithm, a series of the mathematical steps that scamble data, is the underlying mathematical process behind encryption. There are a variety of cryptographic algorithms that have been developed based on different mathematical processes. Some algorithms result in stronger encryption than others-the stronger the algorithm, the more difficult the encrypted data is to crack.
• There are two broad classes of encryption systems:
i. Symmetric: In a symmetric crypto-system, either the encryption key and decryption key are the same or one is easily derivable from the other. For example, include Advanced Encryption Standard (AES) and Data Encryption Standard (DES).
⤏ Traditional cryptography: Traditional cryptography (secret key cryptography or symmetric cryptography) involves a private or secret key that was shared by the individuals involved in the transmission. The key is a mathematical entity that the sender can use to encrypt a message and the receiver can use to decrypt it. The main problem with this type of cryptography is that how the owner of the key can securely transmit the key to those who will need it to decrypt messages sent to them.
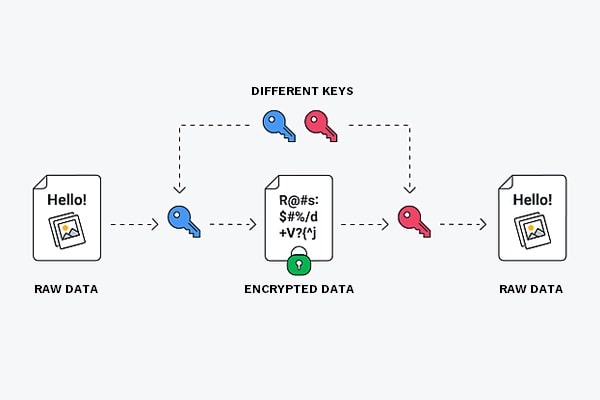
ii. Asymmetric: In an asymmetric crypto-system, on the other hand, the decryption key is not equal to the encryption key. Furthermore, it is computationally impact to derive a decryption key from the encryption key. For example, RSA (Rivest-Shamir-Adleman) and Elliptic Curve Cryptography (ECC). The two keys in a pair are as follows:
⤏ Private key: A private key is known only to the owner (or the owner's client program), and its used for decryption and for signing digital signatures. The private key should be securely stored and not shared with others. If someone possesses the private key corresponding to a particular public key, they can decrypt messages encrypted with that public key.
In the example above, Person B, who owns the private key corresponding to the public key shared with Person A, uses their private key to decrypt the message received from Person A.
⤏ Public key: (asymmetric crypto-system) solves this problem by creating a set of two different keys for anyone needing to transmit encrypted information. A precise mathematical relationship exists between the two keys, which together are called a key pair. Both the keys are produced at the same time using an algorithm. As a result, when either one of two keys is used to encrypt a message, the other can be used to decrypt it.
A public key is distributed to any user (or to any client program) who requests it. Because the public and private keys are related mathematically calculation on it and extract the corresponding private key. Therefore, use keys sufficiently long and with a sufficiently complex mathematical relationship so that it is all but impossible to extract the private key from the public one.
Once a key pair is generated for someone, he/she can use it to encrypt messages and digitally sign messages so that the recipient can be sure of the identity of the sender.
The whole public key cryptography system is founded on trust. All persons who are issued key pairs must trust the third-party authority who provided the key pairs. This trusted authority is called a Certificate Authority (CA). Someone who wants to obtain a key pair from a CA must contract CA and present proof of identity. This could involve a face-to-face meeting, examination of a driver's license with a photograph, or some other method of establishing a user's identity.
Note: The design and implementation of robust cryptosystems are essential for maintaining the security of sensitive information in today's digital age.
Category: Security
on: 05 Oct 2023
on: 22 Jan 2024
Featured posts
You may like these posts.
What is 5G Network? It's time to upgrade your mobile?
5G is a next-generation high-speed Mobile network connection, that replaces our 4G LTE network connections. Samsung Galaxy S10 5G, first 5G supported mobile.

Programming Generations - 1GL, 2GL, 3GL, 4GL, 5GL, 6GL:
A programming language is a set of written symbols that instructs the computer hardware to perform specific tasks. Programming language consists of a vocabulary.
Basic Concept of Memory Management:
Memory Management is the functionality of an operating system that handles or manages the primary memory and disk during execution.
What's Next?
We've now entered the finance section on this platform, where you can enhance your financial literacy.